Posted: July 28th, 2013 | Author: cj_000 | Filed under: Uncategorized | 10 Comments »
 On Wednesday, July 24th Google launched the Chromecast. As soon as the source code hit we began our audit. Within a short period of time we had multiple items to look at for when our devices arrived. Then we received our Chromecasts the following day and were able to confirm that one of the bugs existed in the build Chromecast shipped with. From that point on we began building what you are now seeing as our public release package.
On Wednesday, July 24th Google launched the Chromecast. As soon as the source code hit we began our audit. Within a short period of time we had multiple items to look at for when our devices arrived. Then we received our Chromecasts the following day and were able to confirm that one of the bugs existed in the build Chromecast shipped with. From that point on we began building what you are now seeing as our public release package.
Exploit Package:
Our Chromecast exploit package will modify the system to spawn a root shell on port 23. This will allow researchers to better investigate the environment as well as give developers a chance to build and test software on their Chromecasts. For the normal user this release will probably be of no use, for the rest of the community this is just the first step in opening up what has just been a mysterious stick up to this point. We hope that following this release the community will have the tools they need to improve on the shortfalls of this device and make better use of the hardware.
Is it really ChromeOS?
No, it’s not. We had a lot of internal discussion on this, and have concluded that it’s more Android than ChromeOS. To be specific, it’s actually a modified Google TV release, but with all of the Bionic / Dalvik stripped out and replaced with a single binary for Chromecast. Since the Marvell DE3005 SOC running this is a single core variant of the 88DE3100, most of the Google TV code was reused. So, although it’s not going to let you install an APK or anything, its origins: the bootloader, kernel, init scripts, binaries, are all from the Google TV.
We are not ruling out the ability for this to become a Google TV “stick”.
Speaking of Google TV – if you are in Vegas for DEF CON 21, check out our talk – “Google TV: Or How I Learned to Stop Worrying and Exploit Secure Boot” this Friday August 2nd at 3PM in the Penn and Teller Theater! We’ve got secure boot exploits for the Google TV (unsigned kernels and roots anyone?) and more – don’t miss it!

How does the exploit work?
Lucky for us, Google was kind enough to GPL the bootloader source code for the device. So we can identify the exact flaw that allows us to boot the unsigned kernel. By holding down the single button, while powering the device, the Chromecast boots into USB boot mode. USB boot mode looks for a signed image at 0×1000 on the USB drive. When found, the image is passed to the internal crypto hardware to be verified, but after this process the return code is never checked! Therefore, we can execute any code at will.
ret = VerifyImage((unsigned int)k_buff, cpu_img_siz, (unsigned int)k_buff);
The example above shows the call made to verify the image, the value stored in ret is never actually verified to ensure that the call to “VerifyImage” succeeded. From that, we are able to execute our own kernel. Hilariously, this was harder to do than our initial analysis of exploitation suggested. This was due to the USB booted kernel needing extra modifications to allow us to modify /system as well as a few other tweaks.
We then built a custom ramdisk which, when started, began the process of modifying the system by performing the following steps:
- Mount the USB drive plugged in to the chromecast.
- Erase the /system partition (mtd3).
- Write the new custom system image.
- Reboot.
Note: /system is squashfs as opposed to normally seen EXT4/YAFFS2.
The system image installed from our package is a copy of the original with a modified /bin/clear_crash_counter binary. This binary was modified to perform its original action as well as spawn a telnet server as root.
After the above process, the only modification to the device is done to spawn a root shell. No update mitigations are performed which means that theoretically, an update could be pushed at any moment patching our exploit. Even with that knowledge, having an internal look at the device is priceless and we hope that the community will be able to leverage this bug in time.
Downloads and instructions for exploitation can be found on our wiki at: GTVHacker Wiki: Google Chromecast
Looking for help rooting your device or just want to ask us a question? Check out our Chromecast forum
Posted: August 4th, 2012 | Author: zenofex | Filed under: Uncategorized | Comments Off on GTVHacker at DEF CON 20: Oh the Exploits!
As previously mentioned, we were invited to speak at the DEFCON 20 security conference, covering what else – Hacking the Google TV. We all had an awesome time at DEFCON and it was great to meet the rest of the team, both current and past members.
If you haven’t seen our slides from our DEFCON 20 presentation you can find them online here
If you notice in the DEFCON slides, we released multiple exploits, including:
WARNING: The links above contain the until now unreleased Revue root. As bliss described it, “it is like punching the device in the face while telling it that it’s not getting hit”. It is incredibly unstable and we are providing it unpackaged to prevent it from being used by someone who may end up damaging their box. If you are looking to get root to help achieve some form of optimal Android experience from the box, then please wait for a better packaged version with persistence. If you are technically savy and are willing to risk damaging your box, gambling on how skilled you are, then feel free to give it a shot. We will note that you are likely to brick your device much like we have bricked ours (but we have fancy-pants hardware recovery mechanisms).
The Revue root is an interesting one, at the moment it is not persistent; upon each reboot the Revue will need to be rooted again. We are working constantly to get past this road block. Unfortunately, every last item on the box has a signature that is verified at boot, so it makes keeping root across boots difficult. However, rest assured – we will do our best to get some form of persistence out soon. In the meantime, if you are worried, just unplug your Revue from the Internet.
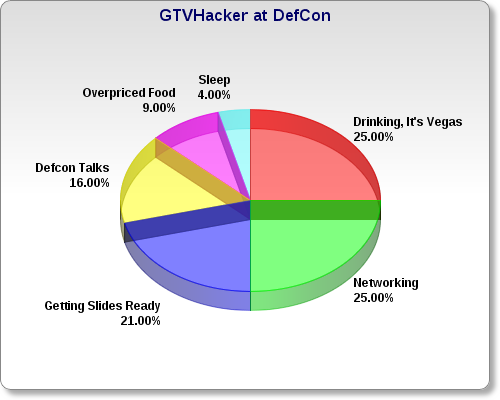
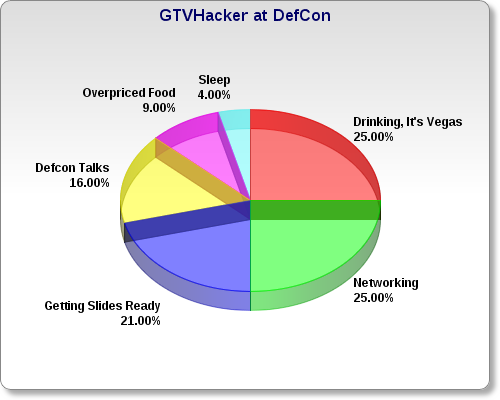
Finally – we kept track of what we did while at the conference, and roughly how much time everything took:
Posted: July 23rd, 2012 | Author: zenofex | Filed under: Uncategorized | 2 Comments »
A few members of the GTVHacker team will be presenting at the Defcon security conference in Las Vegas this week regarding our newest exploits for the gen-1 GoogleTV line. If you are nearby come check out our talk schedule for Sunday July 29th 3:00pm. A brief description of the talk and info on the presenters can be found on the Defcon Speakers page:
“The GoogleTV platform is designed to bring an integrated web experience, utilizing the Chrome web browser and Android applications, to your television. GoogleTV is based on the Android operating system, which is mainly used in tablets and smart phones, but customized with security features not normally seen on most Android devices. The current version of the platform utilizes signatures to establish a “chain of trust” from bootloader to system applications.
This presentation will focus on the current GoogleTV devices, including X86 platform details, and the exhaustive security measures used by each device. The presentation will also include video demonstrations of previously found bugs and exploits for each GoogleTV device and includes specific details about how each bug works. Furthermore, we will include interesting experiences that the team has encountered along the way. Finally the talk will be capped off with the release of multiple unpublished GoogleTV exploits which will allow unsigned kernels across all x86 devices (Revue / Sony GoogleTV).”
We also have other surprises in store for the community. Make sure to check out our presentation if you are at or around Defcon, otherwise check our twitter (@GTVHacker) and blog after the conference for public releases.
Posted: July 6th, 2012 | Author: zenofex | Filed under: Uncategorized | Comments Off on New Wiki Updates – featuring Sony NSZ-GS7 Teardown
 It’s been a bit since we’ve made a blog post, however exciting times are coming. To
It’s been a bit since we’ve made a blog post, however exciting times are coming. To
start, we have cleaned up the wiki and reorganized some sections. The NSZ-GS7 section of our wiki has been updated with lots
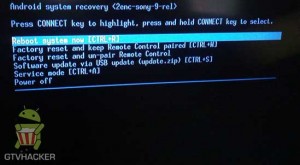
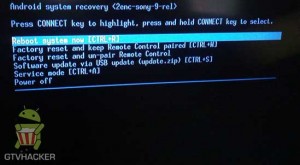
of new info, including a tear down and pictures of the new Sony recovery. You can check the teardown pics and the new recovery out here:
GTVHacker Wiki: Sony NSZ-GS7
We’ve also started a page for the new LG devices, the LG 47g2 and the 55g2. The LG section is lacking since none of the GTVHacker team members currently have the TV, so we are counting on the community to fill in the blanks. We are also looking for a few users to help us with some remote debugging of the TV. If you’d like to help out you can find a few things we are looking for on our forums in the new LG section at:
GTVHacker Forums: LG 47g2 and 55g2
Posted: February 20th, 2012 | Author: zenofex | Filed under: Uncategorized | 2 Comments »

We give to you our latest release, a root for all current Sony Google TV devices that we call “The GTVHacker Sony Recovery Downgrader & Rebooter”. This method will allow you root and run custom unsigned kernels on your Sony Google TV device.
The process in the guide above will walk you through downgrading the system to an exploitable version. Then using another exploit, we hijack the devices boot process and reload a new kernel. This completely bypasses the signatures normally used by the system, including those used in the bootloader, kernel, and init binary. The kernel reload process happens automatically each time the box is powered on, and the USB drives required for the install are not needed again. After loading our attached unsigned kernel you will notice a new splash screen (featuring the Sony and GTVHacker logo) as well as the following perks:
- Modified flash plugin with random per box flash string for Content Provider Bypass.
- Crippled update feature to prevent box from receiving automatic updates.
- Completely RW system, cache, and rootfs partitions
- Full ADB Root
- Removed signature checks on kernel / init scripts / init binary
- A few other surprises.
- BETA: Enable NTFS Support for Sony Google TV devices (see wiki for instructions on how to add: GTVHacker.com: Sony NTFS)
Between the speediness of the 3.2 upgrade and the unsigned kernels we finally have the box that we’ve always wanted from the Google TV. We recommend this update to everyone as it only requires 4 USB sticks and is a 100% softmod (No soldering required!).
The guide and information about the process can be found at our wiki:
How to Root Guide:
GTVHacker.com: Running Unsigned Kernels On Sony GTV
For a more detailed look into how this all works, check out the about:
GTVHacker.com: About The Sony Downgrade & Rebooter (Root)
And finally, for support or to comment checkout our forum post:
GTVHacker Forums: NSX-GT1 and NSZ-GT1 exploit to run unsigned kernels!
GTVHacker
Posted: October 19th, 2011 | Author: resno | Filed under: Uncategorized | Comments Off on Updating to future USB updates from HC “User-Debug” leak
Below is a method to flash the old “un-neutered” HC recovery onto the new userdebug build. This will allow you to update by USB to the official HC build that Google will hopefully release in the coming weeks. The method below requires that you have installed adb from the android sdk. Please make sure to enter the commands below after entering the directory that the recovery.img was extracted to (or to change the “adb push recovery.img /tmp/recovery.img” command to “adb push /path/to/recovery.img /tmp/recovery.img”).
Warning: Using any recovery other than a properly signed recovery will brick your box, only use the recovery supplied. You also may to ensure you have a good network connection to your revue before continuing.
Recovery:
http://www.multiupload.com/BLFDQYH354
Note: recovery.img(sha1) = 14c31dc6db2d8f9ec15f94f2f929dbb68142d16c
Step 1.) Get IP Address of Revue (settings->network->status).
Step 2.) Enable adbd (settings->applications->development), then check “Remote Debugging”.
Step 3.) Add the IP Address of the computer you are connecting from (“Debugger Ip Address in settings->applications->development).
Step 4.) Connect to adb from computer using the following (Replacing with your ip) adb command:
Step 5.) Restart adbd as root by executing the following:
Step 6.) Reconnect to adbd on the revue using:
Step 7.) Paste each line of the following (one at a time).
- adb push recovery.img /tmp/recovery.img
- adb shell flash_image recovery /tmp/recovery.img
Successfully running the last line should output something similar to the following:
- mtd: successfully wrote block at 0
- mtd: successfully wrote block at 40000
- mtd: successfully wrote block at 80000
- mtd: successfully wrote block at c0000
- mtd: successfully wrote block at 100000
- mtd: successfully wrote block at 140000
- mtd: successfully wrote block at 180000
- mtd: successfully wrote block at 1c0000
- mtd: successfully wrote block at 200000
- mtd: successfully wrote block at 240000
- mtd: successfully wrote block at 280000
- mtd: successfully wrote block at 2c0000
- mtd: successfully wrote block at 300000
- mtd: successfully wrote block at 340000
- mtd: successfully wrote block at 380000
- mtd: successfully wrote block at 3c0000
- mtd: successfully wrote block at 400000
- mtd: successfully wrote block at 440000
- mtd: successfully wrote block at 480000
- mtd: successfully wrote block at 4c0000
- mtd: successfully wrote block at 500000
- mtd: successfully wrote block at 540000
- mtd: successfully wrote block at 580000
- mtd: successfully wrote block at 5c0000
- mtd: successfully wrote block at 600000
- mtd: successfully wrote block at 0
Posted: August 26th, 2011 | Author: resno | Filed under: Uncategorized | Comments Off on New Devices for UK
Reports are, there are some new devices on the horizon for our friends across the lake. (The Atlantic Lake). Reports arent saying much yet, but GoogleTv isnt going anywhere!
Posted: June 15th, 2011 | Author: resno | Filed under: Uncategorized | Comments Off on Zenofex speaks on podcast
Recently, Zenofex of the GtvHacker community spoke on a podcast about getting root. You can check it out here: http://techmisfits.com/05/19/gtvhacker-zenofex-speaks/.
He speaks with Resno and Integgrol.
Posted: May 10th, 2011 | Author: resno | Filed under: Uncategorized | 1 Comment »
Well, after hearing Google IO, we have learned some unfortunate information. We wont be getting market till sometime this summer.
We are suppose to getting Android version 3.1, which is good news. Not sure what that means in terms of getting and maintaining a software root for the Google Tv Devices.
Stay tuned as more details develop. Soon our hopes and dreams will become a reality. (At least we hope)
Posted: April 8th, 2011 | Author: resno | Filed under: Uncategorized | Tags: google, googletv, sdk, software root | 2 Comments »
We have been wondering when the Google TV SDK would be released and we are starting to hope and think the time is soon-ish. Reports are, it should be release within a month! The market is believed to follow in about 3 months.
This has several implications, but the biggest note is, this should open the door and make the GoogleTV any even better device. Having the market and sdk available will allow us one more tool in finding a software root. This is an exciting time, and we can not wait to ride the rollercoaster.
 On Wednesday, July 24th Google launched the Chromecast. As soon as the source code hit we began our audit. Within a short period of time we had multiple items to look at for when our devices arrived. Then we received our Chromecasts the following day and were able to confirm that one of the bugs existed in the build Chromecast shipped with. From that point on we began building what you are now seeing as our public release package.
On Wednesday, July 24th Google launched the Chromecast. As soon as the source code hit we began our audit. Within a short period of time we had multiple items to look at for when our devices arrived. Then we received our Chromecasts the following day and were able to confirm that one of the bugs existed in the build Chromecast shipped with. From that point on we began building what you are now seeing as our public release package.